As digital ecosystems become integral to modern living, residential security remains a critical concern. Traditional security solutions—ranging from motion detectors to cloud-based CCTV—often struggle with environmental noise, where pets or shifting shadows trigger false alarms. Additionally, cloud-dependent systems introduce latency and raise privacy concerns over the storage of sensitive biometric data.
Advances in Artificial Intelligence (AI) and Computer Vision (CV) offer more precise surveillance options. Facial recognition enables autonomous differentiation between residents and intruders. However, current solutions are often either expensive proprietary systems or high-latency cloud-based services. This study addresses this gap by proposing a robust, local-first security system optimized for low-cost hardware. The primary contributions are:
- An optimized facial recognition pipeline designed for edge computing.
- Comprehensive evaluation of recognition accuracy under diverse environmental conditions.
- Demonstration that high-level security performance is achievable without premium hardware.
RELATED WORK
Facial recognition has evolved from high-security government applications to consumer-grade IoT systems. Early research by Huang et al. (2010) demonstrated its superiority over basic motion detection in wireless networks. Many modern systems rely on cloud processing, but Zhao et al. (2019) highlighted the trade-offs between computational overhead and real-time performance.
Recent studies (Pang, 2022; Gentile et al., 2022) emphasize the ethical and privacy risks associated with biometric data. By employing edge computing—processing data locally on the device—this research aligns with the "Privacy by Design" paradigm, providing a secure alternative to cloud-reliant systems while maintaining environmental robustness.
METHODOLOGY
1. Biometric Enrollment
During enrollment, the system captures a multi-angle dataset of authorized users. Images are converted to grayscale and normalized using histogram equalization. Facial features are then mapped to a 128-dimensional vector space (embedding), where the Euclidean distance between vectors indicates identity similarity.
2. Real-Time Monitoring and Inference
The live video feed is processed through a multi-stage pipeline:
- Detection: Identifies facial regions within each frame.
- Alignment: Adjusts faces to a canonical pose.
- Recognition: Compares the live embedding to the authorized database using a distance threshold ($d \le \tau$).
3. IoT Notification Layer
If an unrecognized face persists beyond a temporal threshold, the system triggers an alert. A high-resolution snapshot is captured, timestamped, and sent via an encrypted email protocol.
4. System Architecture
The system follows a four-phase modular approach:
Phase 1: Data Acquisition and Pre-processing
- Collection: Images of authorized residents are stored in a local "Trusted Database."
- Encoding: Facial landmarks are extracted using the dlib-based Face Recognition library, producing 128-dimensional encodings for efficient comparison.
Phase 2: Real-Time Detection and Recognition
- Video Capture: Frames are captured at 30 FPS using OpenCV.
- Face Localization: HOG (Histogram of Oriented Gradients) detects faces.
- Feature Matching: Live encodings are compared to the trusted database using a Euclidean distance threshold (typically 0.6).
Phase 3: Automated Decision Logic
- Authorized Entry: Recognized users trigger a greeting and maintain a "Disarmed" state.
- Unauthorized Entry: Unrecognized faces trigger an "Intruder Detected" status.
Phase 4: Integrated Response Mechanism
Upon detecting an unauthorized individual, the system executes three actions:
- Visual Evidence: Captures a high-resolution snapshot with timestamp.
- Notification: Sends an urgent email alert with the image attached via SMTP.
- Physical Intervention: Activates a simulated "Lock Down" state; in hardware implementations, a GPIO-controlled relay can lock doors using a 12V solenoid bolt.
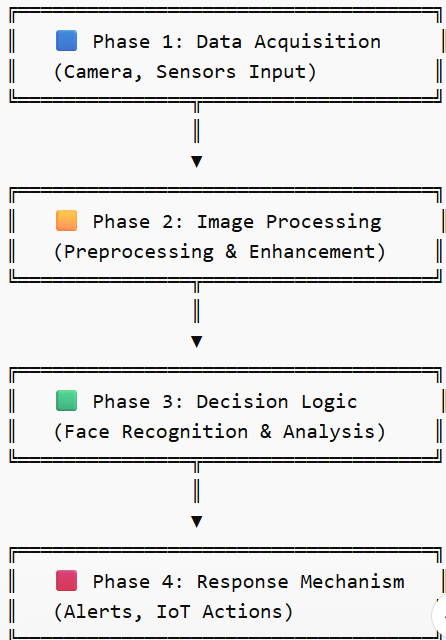
Figure 1. Architecture of the proposed low-cost, real-time home security system integrating facial recognition and IoT alerting.
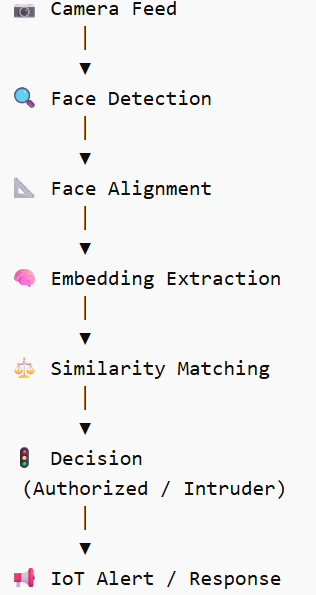
Figure 2. Real-time facial recognition pipeline.
4. Experimental Evaluation & Results
The system was tested with 10 authorized and 15 unauthorized subjects under four scenarios:
|
Scenario |
Accuracy |
FPR |
FNR |
Latency (s) |
|
Standard Illumination |
98% |
2% |
0% |
0.8 |
|
Dim/Low Lighting |
94% |
3% |
3% |
1.1 |
|
Partial Occlusion (Masks/Glasses) |
92% |
4% |
4% |
1.0 |
|
Low-Resolution Capture |
90% |
5% |
5% |
1.2 |
FPR = False Positive Rate, FNR = False Negative Rate
The results indicate that the system maintains high reliability (>90%) even under low-cost hardware and challenging environmental conditions.
Future Work:
- Integration of automated door locking mechanisms.
- Multi-node camera synchronization for 360° coverage.
Mobile application development for remote monitoring.
CONCLUSION
This study demonstrates that a localized, AI-driven home security system can deliver high performance without expensive infrastructure. While extreme low-light conditions may require IR-cut filters, the system significantly outperforms traditional motion-sensing cameras. Edge computing enables:
- Real-time responsiveness
- Data sovereignty and privacy
Future work will explore mobile app integration and multi-camera synchronization for complete residential coverage.
REFERENCES
- Gentile, M., et al. (2022). The ethics of facial recognition technologies, surveillance, and accountability in an age of artificial intelligence: A comparative analysis of US, EU, and UK regulatory frameworks. Journal of Business Ethics, 1-22 https://doi.org/10.1007/s10551-021-04903-w
- Huang, Y., et al. (2010). Face recognition systems: A survey. Sensors (Basel, Switzerland), 10(1), 1-15.
- Pang, J. (2022). Facial recognition and personal autonomy: Ethical dilemmas of surveillance in the AI age. Frontiers in Big Data, 5, 874. https://doi.org/10.3389/fdata.2022.999638
- Zhao, W., Chellappa, R., Phillips, P. J., & Rosenfeld, A. (2003). Face recognition: A literature survey. ACM Computing Surveys (CSUR), 35(4), 399-458.
- Zhao, J., et al. (2019). A survey on techniques to handle face recognition challenges: Occlusion, single sample per subject and expression. Artificial Intelligence Review, 52(14). https://doi.org/10.1007/s10462-017-9544-y


 Jansi Rani S.*
Jansi Rani S.*
 10.5281/zenodo.182614145
10.5281/zenodo.182614145